NSA Releases Christmas Eve Surprise
WHISTLEBLOWING - SURVEILLANCE, 29 Dec 2014
Murtaza Hussain – The Intercept
26 Dec 20145 – The National Security Agency on Christmas Eve day released twelve years of internal oversight reports documenting abusive and improper practices by agency employees. The heavily redacted reports to the President’s Intelligence Oversight Board found that NSA employees repeatedly engaged in unauthorized surveillance of communications by American citizens, failed to follow legal guidelines regarding the retention of private information, and shared data with unauthorized recipients.
While the NSA has come under public pressure for openness since high-profile revelations by whistleblower Edward Snowden, the release of the heavily redacted internal reports at 1:30PM on Christmas Eve demonstrates limits to the agency’s attempts to demonstrate transparency. Releasing bad news right before a holiday weekend, often called a “Christmas Eve surprise,” is a common tactic for trying to minimize press coverage.
The reports, released in response to a Freedom of Information Act request submitted by the American Civil Liberties Union, offer few revelations, but contain accounts of internal behavior embarrassing to the agency. In one instance an NSA employee “searched her spouse’s personal telephone directory without his knowledge to obtain names and telephone numbers for targeting”, a practice which previous reports have indicated was common enough to warrant the name “LOVEINT”.
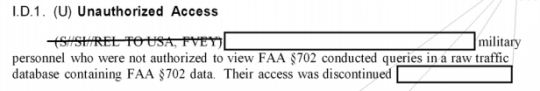
Many of the reports appear to deal with instances of human error rather than malicious misuse of agency resources. Nonetheless, many of these errors are potentially serious, including entries suggesting that unminimized U.S. telephone numbers were mistakenly disseminated to unauthorized parties and that military personnel were given unauthorized access to raw traffic databases collected under the Foreign Intelligence Services Act.
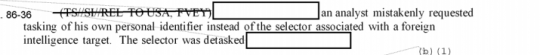
There are also accounts of simple bumbling by NSA employees, including the apparently common mistake of targeting their own communications for surveillance. In one unintentionally amusing passage, an NSA analyst is said to have “targeted his personal cellphone,” because he “mistakenly thought it would be acceptable to [redacted].” Another common example is the practice of NSA analysts accidentally designating their own communications as being those of a foreign intelligence target.
Even in their redacted form the reports give insight into the level of power individual agency employees have in ordering surveillance, and the intentional and unintentional abuses that can take place in an environment of minimal oversight. Though NSA officials have repeatedly suggested that the agency has rigorous safeguards in place to prevent individual employees from abusing their powers of surveillance, the agency’s own confidential internal reporting appears to contradict this.
“The government conducts sweeping surveillance under this authority -— surveillance that increasingly puts Americans’ data in the hands of the NSA”, Patrick Toomey of the ACLU’s National Security Project said in comments to Bloomberg News. “Despite that fact, this spying is conducted almost entirely in secret and without legislative or judicial oversight.”
_______________________________
Email the author: murtaza.hussain@theintercept.com
Go to Original – firstlook.org
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.
Read more
Click here to go to the current weekly digest or pick another article:
WHISTLEBLOWING - SURVEILLANCE: