New Film Tells the Story of Edward Snowden; Here Are the Surveillance Programs He Helped Expose
WHISTLEBLOWING - SURVEILLANCE, 19 Sep 2016
Jenna McLaughlin and Talya Cooper – The Intercept
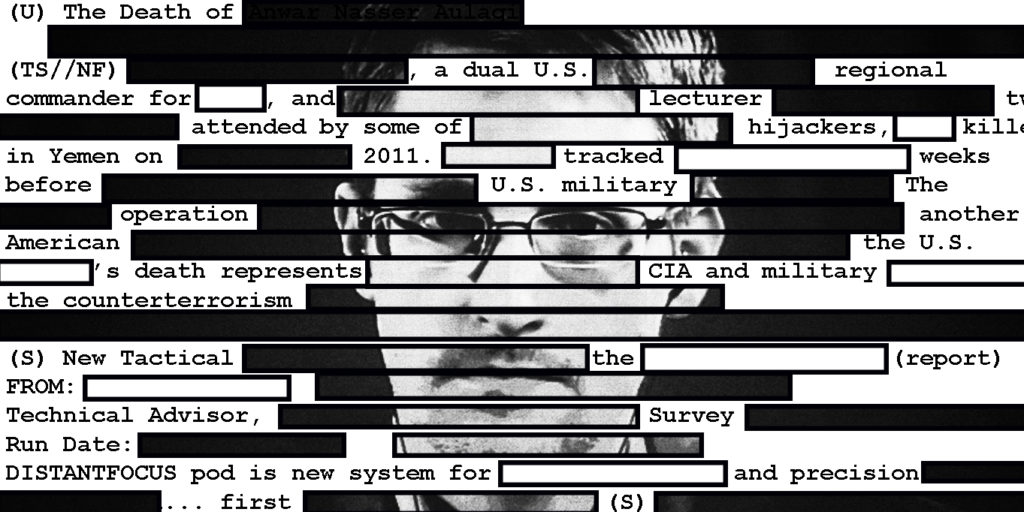
16 Sep 2016 – Oliver Stone’s latest film, “Snowden,” bills itself as a dramatized version of the life of Edward Snowden, the NSA whistleblower who revealed the global extent of U.S. surveillance capabilities.
Stone’s rendering of Snowden’s life combines facts with Hollywood invention, covering Snowden being discharged from the military after an injury in basic training, meeting his girlfriend, and training in the CIA with fictitious mentors (including Nicolas Cage’s character, most likely a composite of whistleblowers like Thomas Drake and Bill Binney). Snowden then goes undercover, only to see an op turn ugly; becomes a contractor for the CIA and NSA; and finally chooses to leave the intelligence community and disclose its vast surveillance apparatus, some of which he helped develop.
The movie hits key points in Snowden’s story, including his growing interest in constitutional law and the Foreign Intelligence Surveillance Court, some of the U.S. surveillance programs he eventually unmasked, and parts of his furtive meetings in Hong Kong with Glenn Greenwald and Laura Poitras (co-founders of The Intercept), as well as The Guardian’s Ewen MacAskill.
There are doses of artistic license — for example, a Rubik’s Cube hiding the drive where he stored the documents, and Snowden’s CIA mentor spying on his girlfriend through her webcam. In hazier focus are the global questions his revelations raised, including the legal and moral implications of the U.S. government collecting data on foreigners and Americans with relative impunity, and the very real stories born of Snowden’s massive disclosures.
So here’s a retrospective of sorts for moviegoers and others interested in the journalism Edward Snowden made possible through his decision to become a whistleblower: In all, over 150 articles from 23 news organizations worldwide have incorporated documents provided by Snowden, and The Intercept and other outlets continue to mine the archive for stories of social and political significance.
In the hope that Stone’s movie will spark more widespread interest in the NSA programs Snowden helped bring to light, The Intercept has compiled its stories based on the archive of documents, which can be explored through the chart below.
Since the first revelations from Snowden were published in Glenn Greenwald’s June 6, 2013, Guardian article, “NSA Collecting Phone Records of Millions of Verizon Customers Daily,” nearly 1,200 documents from Snowden’s disclosures have been released to the public. These include fragments of the “black budget,” a secret document presented to Congress by intelligence agencies, images hacked from drone feeds, and PowerPoint presentations that painstakingly detail the technology behind the NSA’s surveillance efforts.
The Intercept and other outlets have reported extensively on some of the major technical programs mentioned during the film — PRISM and Upstream, both authorized under Section 702 of the Foreign Intelligence Surveillance Act. PRISM vacuums up hundreds of millions of internet communications every day from the people it “targets,” and those they communicate with — as well as some irrelevant communications it picks up “incidentally” because of the way the technology works. It’s unclear how many of those communications belong to Americans. Upstream gathers communications while they’re traveling through the cables of the internet — voice, text, and more. In the movie, Snowden gets a glimpse at these programs while going undercover for the CIA.
When Snowden shares a map with a few of his colleagues displaying data on surveillance conducted within different countries, the film is likely nodding toward a program called Boundless Informant — another one of the first Snowden stories reported by Greenwald and MacAskill. The NSA denied at the time that it could determine with absolute certainty “the identity or location” of all the communications it collected — but the program gave it a general sense of the volume of information it got from each country, appearing like a sort of heat map. The U.S. was not, like the movie suggests, the country where the NSA collected the most information; there were many more intercepts from Iran, at least during the time period reported on by The Guardian.
The Intercept debuted its Snowden coverage with a February 10, 2014, article by Jeremy Scahill and Glenn Greenwald titled “The NSA’s Secret Role in the U.S. Assassination Program.” Since then, we have published at least 50 other pieces based on documents from the Snowden archive.
In July 2015, The Intercept delved into one of the NSA’s central programs, also mentioned in the film, called XKeyscore. The program runs like a search engine that helps NSA detect, analyze, and extract information from the massive amounts of communications and online information it collects every day through various filters. Otherwise, the sheer volume of information would be overwhelming.
The agency’s use of cellphone and computer hacking for surveillance has been a recurring theme in The Intercept’s reporting on the Snowden documents. In May 2015, Jeremy Scahill and Josh Begley uncovered the CIA and NSA’s joint mission to crack the security of popular consumer products, including Apple’s notoriously secure iPhone. In the movie, Snowden covers his laptop’s webcam, which he knows the NSA is capable of exploiting through a program called QUANTUM. In reality, the NSA has developed malware implants potentially capable of infecting millions of targeted computers covertly, and automated some of the processes involved in the attacks, as Ryan Gallagher and Glenn Greenwald reported in March 2014.
Many news stories from the Snowden archive involve foreign surveillance and the NSA’s partnerships with intelligence agencies from other countries, a subject the Snowden film barely touches — for example, never mentioning the NSA’s close relationship to the British spy agency Government Communications Headquarters (GCHQ); its partnership with countries like Saudi Arabia; or foreign officials’ lack of understanding about their own spies’ connections to the NSA. The film’s only nod to foreign intelligence occurs when Snowden passes off a special microchip to MacAskill, suggesting it might help him learn more about British spying.
The NSA is obviously more than its technical programs and tools. Stone conjures up Snowden’s friends and colleagues at the spy agencies, including T-shirt-wearing hackers, super genius engineers, and domineering bosses. The Intercept’s Peter Maass has written about the human side of the agency, including its resident advice columnist, who went by “Zelda” and answered questions about things like kitchen etiquette and gossip, as well as a columnist with literary ambitions who called himself “the SIGINT Philosopher.”
Ultimately, the movie reflects Stone’s image of the life of an NSA contract employee. For a real window into the agency, there may be no better resource than the NSA’s own documents. In May 2016, The Intercept began the first concerted effort to make large portions of the Snowden archive available to the public with the release of a set of SIDtoday newsletters, the internal news organ of the Signals Intelligence Directorate at the NSA. The batch releases are ongoing and will likely constitute one of the largest single collections of NSA files.
________________________________
Jenna McLaughlin – ✉jenna.mclaughlin@theintercept.com
Talya Cooper – ✉talya.cooper@firstlook.org
Go to Original – theintercept.com
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.
Read more
Click here to go to the current weekly digest or pick another article:
WHISTLEBLOWING - SURVEILLANCE: