“Russian Hacking”: NATO PsyOp Revealed
SPECIAL FEATURE, 28 Dec 2020
Swiss Policy Research - TRANSCEND Media Service
December 2020 – The “Russian hacking” NATO psyop has finally been solved.
To professional analysts, it has long been clear that the “Russiagate” saga – including the “Russian hacking” claims, the Trump-Russia collusion claims, as well as the “Skripal poisoning incident” and the more recent “Navalny poisoning incident” – has been a US and NATO psychological operation aimed at containing a resurgent Russia and a somewhat unpredictable US President.
Several aspects of the “Russian hacking” psychological operation had already been uncovered by independent researchers like Stephen McIntyre, “Adam Carter” and “The Forensicator”. In early November, however, British researcher David J. Blake essentially solved the “Russian hacking” psyop, down to the operational level, as described in his new book “Loaded for Guccifer 2.0”.
Blake shows how the “Russian hacking” psyop was initiated by the US and NATO in 2014 in response to Russia’s reaction to the US regime change in Ukraine, when Russia retook control of the Crimean Peninsula and supported the de-facto secession of Russian-speaking eastern Ukraine.
The US/NATO psyop was inspired by the actual amateur hackers “CyberBerkut” in Ukraine and “Guccifer” in Romania. Blake shows how in 2014, NATO created a “Cyber Defence Trust Fund” and used this entity to initiate false-flag “hacking operations” against the US and other NATO members that would then be falsely “attributed” to alleged Russian “state-sponsored hacking groups”.
Regarding the most prominent case, the alleged “hacking” of the US Democratic Party (DNC) and the 2016 Hillary Clinton presidential campaign, Blake shows how the emails and documents in question were in fact exfiltrated by the FBI and FBI cybersecurity contractor CrowdStrike, whose founder, Dmitri Alperovitch, is a Senior Fellow at the US-NATO think tank Atlantic Council. (1)
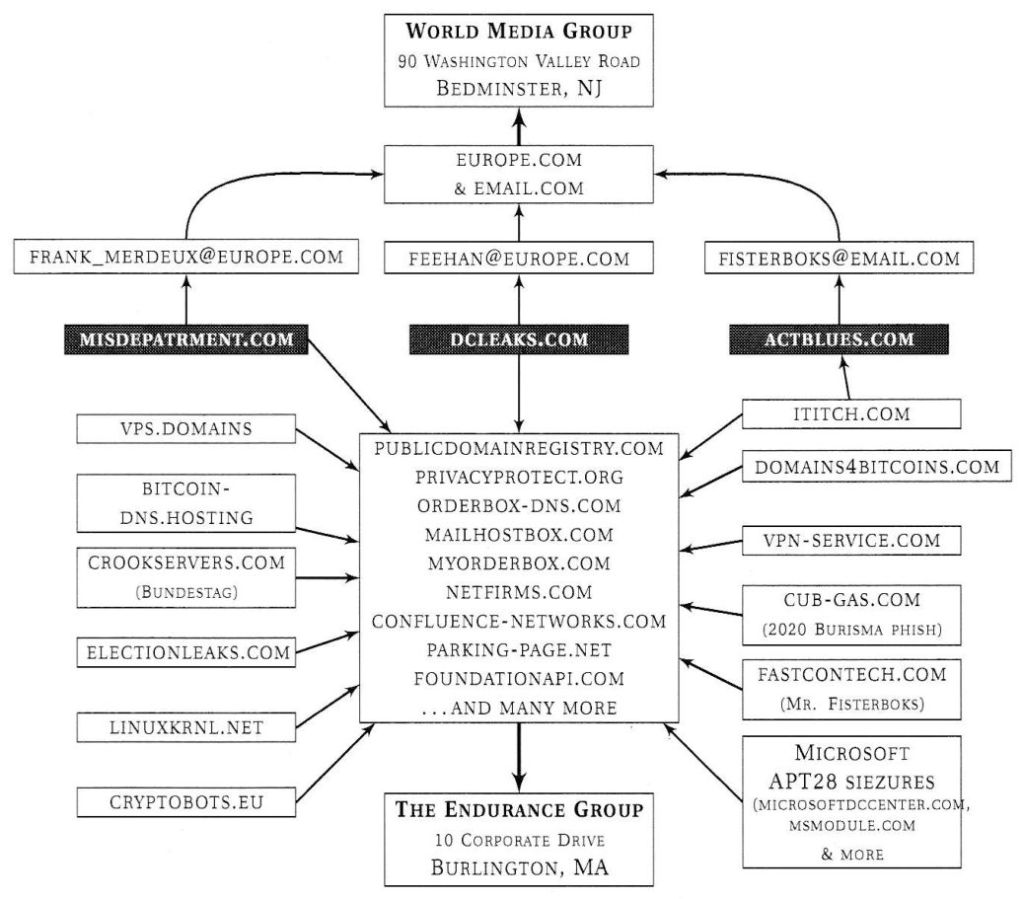
Blake shows how the mysterious persona of Guccifer 2.0, who claimed the hack, was played by none other than Alperovitch himself, while the technical infrastructure, including the notorious website dcleaks.com, was provided by US and NATO intermediaries in NATO member Romania.
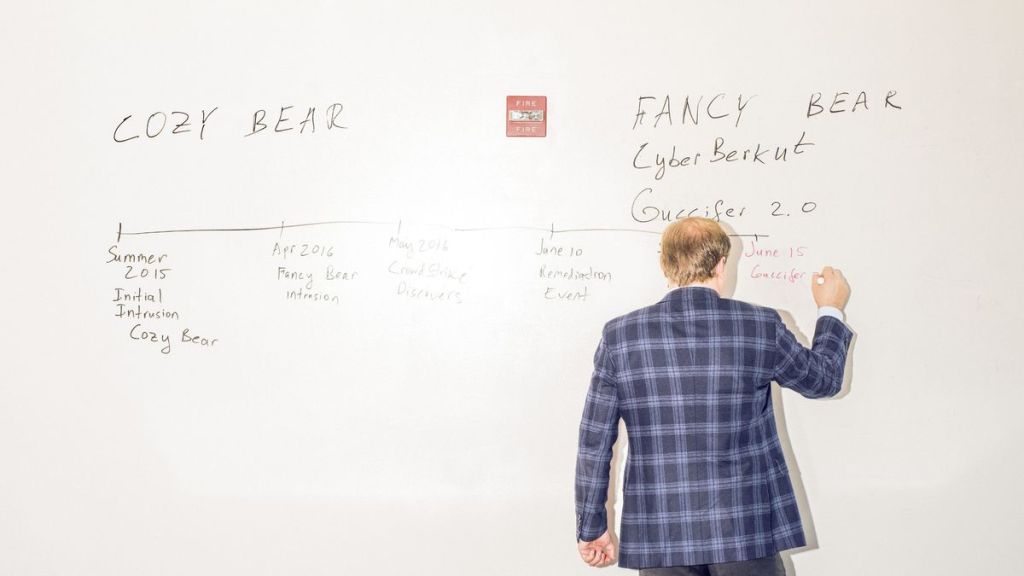
Later, former FBI director Robert Mueller would pretend to “investigate” the cyber operation, attributing it to alleged “Russian hacking groups” named “Cozy Bear” and “Fancy Bear” based on information provided by FBI and DNC contractor CrowdStrike and its CTO Dmitri Alperovitch.
Blake also shows how other alleged “Russian hacks”, including the “hacking” of the German parliament in 2015, relied on the very same NATO-controlled technical infrastructure. Blake was able to show this based on archived information about previous owners of IP addresses, name servers, and SSL security certificates – all pointing to the US military, NATO and the Ukrainian government.
In the case of the staged hack of the US Democratic Party, Blake shows how FBI cybersecurity contractor CrowdStrike added false “Russian fingerprints” by embedding the documents into previously published CyberBerkut documents and inserting additional false signatures. However, CrowdStrike made several technical mistakes that ultimately revealed their US time zone.
Blake highlights the important fact that in all of these false-flag “Russian hacks”, originating from NATO-controlled infrastructure, either no data or only trivial data was released to the public. Some questions continue to remain open, however, such as the role of murdered DNC employee Seth Rich and the actual source of Wikileaks, whose founder Julian Assange is still in British custody.
In the wake of the 2014 US regime change in Ukraine, the family of then Vice President Joe Biden exfiltrated millions of dollars from Ukraine, protected against corruption investigations by Joe Biden himself, as leaked phone recordings confirmed. As of 2021, the professionals behind the Ukraine regime change and the “Russiagate” pysop will once again be in full control of the US government.
Most US and European media have promoted the “Russiagate” and “Russian hacking” psyops and will continue to do so. This is because most US and European media, both liberal and conservative, are themselves embedded in networks linked to NATO and the US Council on Foreign Relations. It is only some independent media that have been seriously investigating these topics.
Are there real Russian state-sponsored hacks against Western targets? Yes. Blake argues that, for instance, the hacking operation against the British Institute for Statecraft and its “Integrity Initiative” – itself deeply involved in the “Russiagate” psyop – was likely a professional Russian operation. The problem is that such real operations are much harder to “attribute” than fake ones.
Besides US and Russian cyber operations, there are also, of course, Chinese operations.
Book: Loaded for Guccifer2.0: Following A Trail of Digital Geopolitics (2020) by David J. Blake
(1) Another well-known Senior Fellow at the Atlantic Council is Eliot Higgins, founder of the Bellingcat group, which apparently serves as a civilian front organization of British military intelligence and was involved in psychological operations both in Ukraine and the Syria war.
__________________________________________
 Swiss Policy Research, founded in 2016, is an independent, nonpartisan and nonprofit research group investigating geopolitical propaganda in Swiss and international media. SPR is composed of independent academics that for personal and professional reasons prefer to protect their identities, and receives no external funding; there are no financial sponsors or backers. Our articles have been published or shared by numerous independent media outlets and journalists, among them Julian Assange, and have been translated into more than two dozen languages.
Swiss Policy Research, founded in 2016, is an independent, nonpartisan and nonprofit research group investigating geopolitical propaganda in Swiss and international media. SPR is composed of independent academics that for personal and professional reasons prefer to protect their identities, and receives no external funding; there are no financial sponsors or backers. Our articles have been published or shared by numerous independent media outlets and journalists, among them Julian Assange, and have been translated into more than two dozen languages.
See also:
Tags: Anglo America, BRICS, Conflict, Geopolitics, Hegemony, History, Imperialism, International Relations, Journalism, Media, Military, Violence
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.

The UN will not be able to end war or eliminate nuclear weapons until it Federates which will require a new UN Charter like the Constitution for the Federation of Earth (aka Earth Constitution. The envisioned “new UN” being a Federal government will turn Russia, China, and the USA into the equivalent of Texas, Alabama and California.
However, the “new UN” must outlaw covert agencies like the CIA, FSB, Mossad, etc. This present article about US/NATO false flag psy op in cyberspace/IT is a good example of what must be banned and made a world crime. This type of false flag demonizes Russia and makes it a false enemy of the US. The US routinely invents false “enemies” to keep its War Business in high gear and extremely profitable.
Thanks for this info. Very helpful for us working toward a “new UN” under the Earth Constitution.