The US National-Security State Has an Invisible Army
MILITARISM, 14 Jun 2021
Branko Marcetic interviews William Arkin | Jacobin Magazine – TRANSCEND Media Service
Tens of thousands of Americans work for US military and intelligence agencies, operating domestically under false identities with fake documents and James Bond–style spy gizmos. Why? To allow the national-security state to pursue its forever wars smoothly, forever.

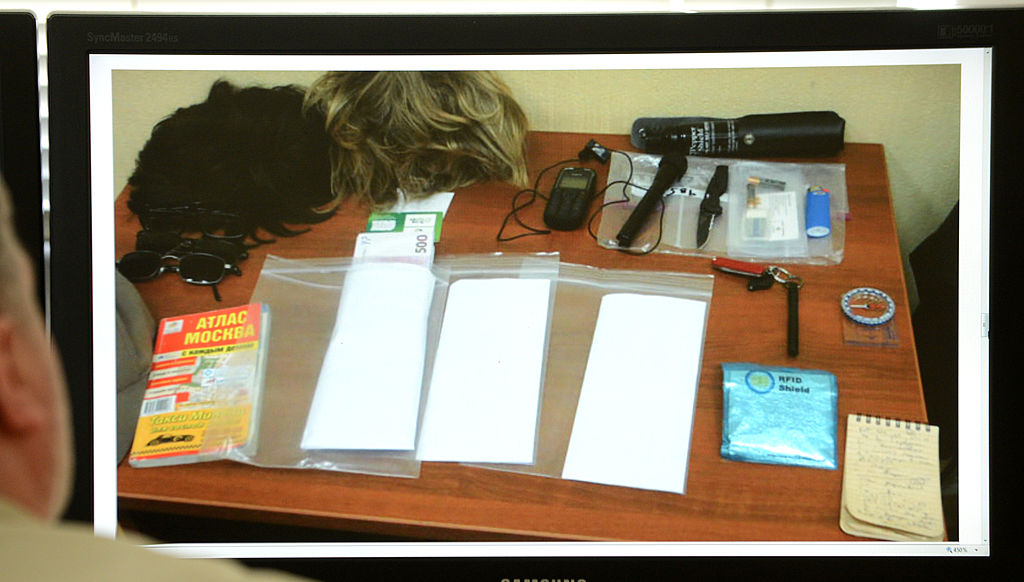
William Arkin exposed the highly classified “signature reduction” program, and the “secret undercover army” of tens of thousands that operates under it, in a recent Newsweek article. (AFP via Getty Images)
9 Jun 2021 – When it comes to the national-security state, the era of big government never ended. As the Edward Snowden revelations and copious other disclosures have shown us over the years, the vast secret state that hums quietly beneath Washington has only grown over the past few decades. But though we get the occasional glimpse of the machine, we’re largely in the dark when it comes to its size and how exactly it operates.
One of those glimpses was recently provided to the public by William Arkin, former US intelligence analyst and veteran journalist who has reported for papers like the Washington Post and the Los Angeles Times, and served for decades as an analyst for NBC until 2019, when he quit over the network’s increasing militarism under Trump. In a May piece for Newsweek, Arkin exposed the highly classified “signature reduction” program, and the “secret undercover army” of tens of thousands that operates under it, sometimes under the US public’s very noses. Jacobin spoke to him about what he found.
************************************
BM: When did you first learn about the signature reduction program? And how did this story come together?
It’s not mentioned in unclassified budget docs, it’s not mentioned in any unclassified regulations, and when I started to do inquiries with the government, they essentially said, “It’s a term that people use, but it’s not an official program.” I knew that was not exactly telling the truth, so that just made me more curious.
As I started to collect more and more resumes and job announcements that describe how many organizations were engaged in signature reduction efforts, and how many companies were involved in providing services to the United States government to achieve signature reduction, I started to contact both individuals and those organizations to see if people would talk to me. I had a lot of lack of success.
But, eventually, I did get a couple of people to start talking, and then they passed me on to other people. People were very reluctant to describe how the techniques of clandestine operations are utilized out there in the world, but they were willing to talk to me in general about the techniques that were being used, many of which I was able to track back to actual spy cases in which spies had been captured and caught, where the details of those cases revealed the techniques and the tradecraft associated with signature reduction.
BM: You write that there are around sixty thousand people who are part of this “secret army,” operating both overseas and domestically. What exactly are they doing?
The first group is the special-operations world, and particularly the clandestine special operations associated with the so-called “black” operations. Well, what keeps them black? It’s all of these techniques of signature reduction, everything from false identities all the way through to civilian cover they’re using to operate in the Middle East and elsewhere in the world. I think there are about thirty thousand or so people who are part of the Navy SEALS, Green Berets, etc., who operate under some level of signature reduction. Not all of them are completely clandestine. And, as I explain in the article, not all of them are even traveling with false identities, but when they get into a country they switch their identities.
The second group is the human intelligence operators at the Defense Department. That also includes people in “close-in surveillance” or “close-in reconnaissance.” For instance, if I want to be able to intercept your signal, I need to get close to you in order to do so, to pick out that signal from the whole variety of signals that are pinging the cell phone tower that you’re communicating with. A lot of that work is done by people who are undercover. This group has been growing since 9/11 and has become a fairly large activity throughout the military.
And the third group are the cyber operators, the people who work online, whether they’re collecting intelligence or monitoring everyone from Al Qaeda and ISIS to the Russians, or are engaged in what are called “influence operations” — propaganda, psychological operations. That’s the fastest-growing group, from utilizing false personas and the very techniques we accuse Russians of using during the 2016 elections, to operating under misdirection or non-attribution, where their identity or their origins as US government cyber operators is obscured. There are more than ten thousand people throughout the NSA and the military who utilize the techniques of signature reduction in this way.
BM: Do we have a sense of what some of these cyber operations look like in concrete terms?
Social media is really an essential part of modern-day operations. Cell phones and social media have become ubiquitous around the world, and in parts of the world where infrastructure isn’t really very good, cell phone and internet services are very important. Most individuals in Africa use their cell phones for banking and commerce. The cell phone is the fabric that ties people together. That world is the avenue by which most people are influenced by false information or through campaigns that communicate with them directly.
It’s important to say that the vast majority of these cyber operations are targeted toward terrorist organizations and adversaries of the United States, from Russia and China all the way down to transnational organized crime organizations. But there’s evidence, too, that the Department of Homeland Security and the US military are increasingly operating online and on social media inside the United States as well.
BM: Does this violate the longstanding bans on the military and US propaganda being deployed domestically?
But, in the modern era, where these types of lines of communication have become so mixed and so varied, I would say that anything that goes out there into public information, that might be propaganda oriented at Russia or China or ISIS, has a greater potential to blow back on the US public and Western public opinion. There’s an increasing danger of American citizens being recipients of this propaganda, and propaganda information being inadvertently plugged back into mainstream media at the same time. That’s really the danger, that with the variety of news media that exists these days, people begin to think that some of the news sources they’re reading are actually independent and nongovernmental.
We see the obvious side of that, for instance, in news channels like Sputnik or RT, which are actually owned by the Russian government. Those sources that are in English are read by a lot of people, and they think it’s somehow independent. Similarly, the United States engages in those same kinds of operations. And given the way most people consume information, particularly because most people get their news from their phones, I think they don’t even recognize the difference between actual news media and sources of propaganda.
The availability of independent information is not lesser, but the variety of propaganda is increasing. And, especially as the mainstream media increasingly goes behind the paywall, people who are out there looking for news, let’s say anti-vaxxers, people skeptical of Covid, or people who are against the government in one way or another, will find online news sources that are less than reliable.
BM: It seems like few people, even in Congress, are familiar with the signature reduction program. What exactly is the level of awareness of it?
I think it really does show you that despite the internet and the fantastic growth of news media, especially all of the new online sources — I’m talking about the Politicos, the Voxes, the Axioses— national security remains as much a black hole as it has always been. And, in that regard, the idea that the internet was going to create citizen journalism, and that journalism would create more transparency, and that transparency would lead to more democracy, has failed.
BM: You make the point that, in a world where we are all surveilled more than ever, to be covert requires the creation of not just false identities but entire social networks that are false. It suggests that a lot more of our online worlds are faker than we might imagine. Is this the case, or am I overstating things?
I’m against censorship of any type. I’m against Donald Trump being censored on Twitter, I’m against Alex Jones being censored from social media. Once we give media companies the authority and encouragement to censor communication, then we’re going down a very bad path. Because then, something that was probably already implicit becomes official, in the sense there’s a sanctioned view of things, and then there’s an unsanctioned view, and the unsanctioned view can’t even be published.
I’m against that, and the so-called “liberal” support for Facebook and other social media companies to restrict communication that they don’t like because it’s “false” is a practice that’s going to come back and bite us in the ass in the future. Whether it’s President Alexandria Ocasio-Cortez or a President Bernie Sanders in the future, it’s going to be interesting to see if the same enthusiasm for censorship exists.
But number two, there’s a claim that I heard from many people that I talked to when I was reporting this article, that, “Oh, you know, human intelligence operations are actually less and less physical and more and more online, because online is more efficient, more productive.” I heard a lot of people living in in the newfangled world say that this newfangled world was going to overtake the old-fashioned world. Here’s the problem with that: we recreate the same dynamics of the trivial being more important than the important.
It’s not like we’re going to get Vladimir Putin, or someone close to him, to be an agent of the CIA, as a source of information and covert action, through Twitter or Facebook or any social media platform. What we’re going to get is a lot of shit, a lot of people who don’t have access to important information, who aren’t really central in government and the military. Then we’re just in a world in which, in a way, ironically, the focus of intelligence becomes to be an influencer, for the CIA to be influencers, to have their own channel.
Then I have to ask, well, influencing what? All of the work the NSA did on ISIS in Syria and Iraq, did any of that have any effect? Because as we’ve seen, though ISIS has maybe lost the physical caliphate in Iraq, it’s growing all over the world. There’s very little evidence to show the gigantic efforts on the part of the US government to increase influence has achieved any goal. We’ve spent billions of dollars on influence annually and everyone hates us.
BM: Do we have a sense of how much of the program is private companies doing the work? And how aware are they of its full scope?
My sense is that very few have a holistic understanding of the size and scope. One organization or one company might be involved in administering some small piece of this, but I found that no one can really make sense of the overall size and scope of signature reduction efforts and their impact.
One source that I talked to at a very high level, a retired officer who had worked in the world of special access programs, had a very good understanding of the size of the effort because he was overseeing that. But, overall, most people I talked to were pretty surprised when I told them of how many companies, how many organizations, how many people worked undercover or availed themselves of signature reduction techniques.
As far as I know, no one in Congress ever had a hearing on the signature reduction effort, or the increasing clandestine nature of military operations, and as far as I know, no one has really written about it ever before. We’re looking at a program that, as far as I can see, has not really gotten any oversight at all, from Congress or from the public-policy world.
BM: In terms of technology, there seemed to be a real contrast between, say, some of the masks that appeared less convincing, and the incredible sophistication of some of the other technologies, like the silicon hand sleeves with false fingerprints.
In the modern era, biometrics has become more and more essential to travel especially. And not just biometrics. For foreigners who enter the United States, I believe they’re now asking for their social media handles.
As identity becomes a matter of record — which is to say that the government records your fingerprints, your signature, your social media identity — then knowing the ecosystem of all of that is essential to be able to thwart it. Many people I talked to were engaged in a lot of research associated with understanding how biometrics work, the purpose of which is to figure out a way to defeat it. If you have any knowledge of the Cold War, for instance, you know that the superpowers engaged in biological and chemical warfare research, always with the justification that they weren’t able to defeat the other guys’ biological weapons unless they themselves understood the technology.
That’s what’s going on in the world of signature reduction: if you don’t understand how the data works, how the information goes from an airport, to the border, back to the intelligence establishment, and so on, how are you going to get somebody into a country, or allow them to operate inside a country clandestinely, in a world in which facial recognition systems, license plate readers, street cameras, doorbell cameras, are taking images of everything of our day-to-day life?
I think what most people don’t understand about surveillance is there’s more information than there are people who can process that information. We have a very distorted view from television and Hollywood. On television I can do a few keystrokes and I know the name of your dog. In real life, even though we have ubiquitous surveillance, most of that data, once it does its basic job — which is to tell you there’s no danger — is more or less lost. It’s not retrievable, it’s not put into a database. When someone enters my gate, the security camera takes a picture and sends me an email. But that’s my own personal system, and I don’t keep the material.
Right now, we live in a world in which there’s far more information than there are people to process it, look at it, or store it. But we are getting to a point where artificial intelligence and unlimited storage will make that information more usable and useful. We are getting there.
BM: What are some of the implications, legal, political, and otherwise, of the existence of this program?
First, I think it shows you the scale and the resilience of the war on terror. I don’t think it’s going to go away anytime soon. Second, it shows you the transformation of the military from the World War II model with metals, if you will, to the modern-day model with information. While we still have battleships and bombers and tanks, they are becoming less and less relevant. This is a window into understanding the transformations of the future.
BM: Is this something the US public should be concerned about, particularly with the push for a domestic “war on terror” since January 6?
I’m somebody who’s been in this world, working both inside government and as a journalist and writer, and I’m not satisfied with the government answer, and nor should the American public. I consider myself their ambassador. If they don’t want to do anything about the government, that’s unfortunate, but I want to provide them with as much information to be able to make an informed decision.
The question that’s interesting in this world is that, as I said earlier, we are on the cusp of understanding the social media era. I don’t think we fully understand it. We don’t understand it in our personal lives — hell, I go to sleep with my goddamn smartphone, and I know there’s something very wrong with that, but I still do! So we haven’t adjusted yet to what it means to live in this modern social media era.
As we determine what the rules of the road are, as we determine the psychological and social and political impacts of the social media era, having our arms around what the government is secretly doing becomes ever more essential. I don’t want the government out there doing secret shit. Period.
_____________________________________________
William Arkin is a former US intelligence analyst and journalist.
Branko Marcetic is a Jacobin staff writer and the author of Yesterday’s Man: The Case Against Joe Biden. He lives in Toronto, Canada.
Tags: Hegemony, Imperialism, Military Industrial Media Complex, Pentagon, Spying, Surveillance, US Military, USA
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.