“Never Be Ashamed:” Why I Decided Not to Delete My Old Internet Posts
MEDIA, WHISTLEBLOWING - SURVEILLANCE, 23 Sep 2019
Edward Snowden – The Intercept
21 Sep 2019 – While working for the National Security Agency, Edward Snowden helped build a system to enable the United States government to capture all phone calls, text messages, and emails. Six years ago, he provided documents about this electronic panopticon to journalists, and the shocking revelations that ensued set off massive changes — changes in attitudes and behaviors, in policies and technologies, across private industry and the public sector, in the U.S. and around the world.
Now, in his new memoir, Permanent Record, Snowden explains how his revolutionary act of whistleblowing came to occur. At its root was a decision dating to Snowden’s earliest contact with the NSA — “the first thing that you might call a principle that occurred to me during this idle but formative time,” as the future government systems engineer puts it in the excerpt below: The determination to live in an honest world, a world where people could show their true faces and own their full history, a world without shame. This was the ideal that guided Snowden into the NSA. And of course it would be the ideal that guided him out, as well.
After my injured legs forced me out of the Army, I still had the urge to serve my country. I would have to serve it through my head and hands — through computing. That, and only that, would be giving my country my best. Though I wasn’t much of a veteran, having passed through the military’s vetting could only help my chances of working at an intelligence agency, which was where my talents would be most in demand and, perhaps, most challenged.
That meant that I needed a security clearance. There are, generally speaking, three levels of security clearance in the American Intelligence Community, or IC: from low to high, confidential, secret, and top secret. The last of these can be further extended with a Sensitive Compartmented Information qualifier, creating the coveted TS/SCI access required by positions with the top-tier agencies — CIA and NSA. The TS/SCI was by far the hardest access to get, but also opened the most doors, and so I went back to Anne Arundel Community College while I searched for jobs that would sponsor my application for the grueling background investigation the clearance required. The approval process for a TS/SCI can take a year or more. All it involves is filling out some paperwork, then sitting around with your feet up and trying not to commit too many crimes while the federal government renders its verdict. The rest, after all, is out of your hands.
Read all our stories from Snowden documents – Snowden Archive
On paper, I was a perfect candidate. I was a kid from a service family, nearly every adult member of which had some level of clearance; I’d tried to enlist and fight for my country until an unfortunate accident had laid me low. I had no criminal record, no drug habit. My only financial debt was the student loan for my Microsoft certification, and I hadn’t yet missed a payment.
None of this stopped me, of course, from being nervous.
I drove to and from classes at community college as the National Background Investigations Bureau rummaged through nearly every aspect of my life and interviewed almost everyone I knew: my parents, my extended family, my classmates and friends. They went through my spotty school transcripts and, I’m sure, spoke to a few of my teachers. I got the impression that they even spoke to a guy I’d worked with one summer at a snow cone stand at Six Flags America. The goal of all this background checking was not only to find out what I’d done wrong, but also to find out how I might be compromised or blackmailed. The most important thing to the IC is not that you’re 100 percent perfectly clean, because if that were the case, they wouldn’t hire anybody. Instead, it’s that you’re robotically honest — that there’s no dirty secret out there that you’re hiding that could be used against you, and thus against the agency, by an enemy power.
I didn’t want to live in a world where everyone had to pretend that they were perfect, because that was a world that had no place for me or my friends.
This, of course, set me thinking — sitting stuck in traffic as all the moments of my life that I regretted went spinning around in a loop inside my head. Nothing I could come up with would have raised even an iota of eyebrow from investigators who are used to finding out that the middle-aged analyst at a think tank likes to wear diapers and get spanked by grandmothers in leather. Still, there was a paranoia that the process created, because you don’t have to be a closet fetishist to have done things that embarrass you and to fear that strangers might misunderstand you if those things were exposed. I mean, I grew up on the Internet, for Christ’s sake. If you haven’t entered something shameful or gross into that search box, then you haven’t been online very long — though I wasn’t worried about the pornography. Everybody looks at porn, and for those of you who are shaking your heads, don’t worry: Your secret is safe with me. My worries were more personal, or felt more personal: the endless conveyor belt of stupid jingoistic things I’d said, and the even stupider misanthropic opinions I’d abandoned, in the process of growing up online. Specifically, I was worried about my chat logs and forum posts, all the supremely moronic commentary that I’d sprayed across a score of gaming and hacker sites. Writing pseudonymously had meant writing freely, but often thoughtlessly. And since a major aspect of early Internet culture was competing with others to say the most inflammatory thing, I’d never hesitate to advocate, say, bombing a country that taxed video games, or corralling people who didn’t like anime into reeducation camps. Nobody on those sites took any of it seriously, least of all myself.
When I went back and reread the posts, I cringed. Half the things I’d said I hadn’t even meant at the time — I’d just wanted attention — but I didn’t fancy my odds of explaining that to a gray-haired man in horn-rimmed glasses peering over a giant folder labeled PERMANENT RECORD. The other half, the things I think I had meant at the time, were even worse, because I wasn’t that kid anymore. I’d grown up. It wasn’t simply that I didn’t recognize the voice as my own — it was that I now actively opposed its overheated, hormonal opinions. I found that I wanted to argue with a ghost. I wanted to fight with that dumb, puerile, and casually cruel self of mine who no longer existed. I couldn’t stand the idea of being haunted by him forever, but I didn’t know the best way how to express my remorse and put some distance between him and me, or whether I should even try to do that. It was heinous, to be so inextricably, technologically bound to a past that I fully regretted but barely remembered.
This might be the most familiar problem of my generation, the first to grow up online. We were able to discover and explore our identities almost totally unsupervised, with hardly a thought spared for the fact that our rash remarks and profane banter were being preserved for perpetuity, and that one day we might be expected to account for them. I’m sure everyone who had an Internet connection before they had a job can sympathize with this — surely everyone has that one post that embarrasses them, or that text or email that could get them fired.
My situation was somewhat different, however, in that most of the message boards of my day would let you delete your old posts. I could put together one tiny little script — not even a real program — and all of my posts would be gone in under an hour. It would’ve been the easiest thing in the world to do. Trust me, I considered it.
But ultimately, I couldn’t. Something kept preventing me. It just felt wrong. To blank my posts from the face of the earth wasn’t illegal, and it wouldn’t even have made me ineligible for a security clearance had anyone found out. But the prospect of doing so bothered me nonetheless. It would’ve only served to reinforce some of the most corrosive precepts of online life: that nobody is ever allowed to make a mistake, and anybody who does make a mistake must answer for it forever. What mattered to me wasn’t so much the integrity of the written record but that of my soul. I didn’t want to live in a world where everyone had to pretend that they were perfect, because that was a world that had no place for me or my friends. To erase those comments would have been to erase who I was, where I was from, and how far I’d come. To deny my younger self would have been to deny my present self’s validity.
I decided to leave the comments up and figure out how to live with them. I even decided that true fidelity to this stance would require me to continue posting. In time, I’d outgrow these new opinions, too, but my initial impulse remains unshakable, if only because it was an important step in my own maturity. We can’t erase the things that shame us, or the ways we’ve shamed ourselves, online. All we can do is control our reactions — whether we let the past oppress us, or accept its lessons, grow, and move on.
This was the first thing that you might call a principle that occurred to me during this idle but formative time, and though it would prove difficult, I’ve tried to live by it.
We can’t erase the things that shame us, or the way we’ve shamed ourselves, online. All we can do is control our reactions.
Believe it or not, the only online traces of my existence whose past iterations have never given me worse than a mild sense of embarrassment were my dating profiles. I suspect this is because I’d had to write them with the expectation that their words truly mattered — since the entire purpose of the enterprise was for somebody in Real Life to actually care about them, and, by extension, about me.
I’d joined a website called HotOrNot.com, which was the most popular of the rating sites of the early 2000s, like RateMyFace and AmIHot. (Their most effective features were combined by a young Mark Zuckerberg into a site called FaceMash, which later became Facebook.) HotOrNot was the most popular of these pre-Facebook rating sites for a simple reason: It was the best of the few that had a dating component.
Basically, how it worked was that users voted on each other’s photos: Hot or Not. An extra function for registered users such as myself was the ability to contact other registered users, if each had rated the other’s photos Hot and clicked “Meet Me.” This banal and crass process is how I met Lindsay Mills, my partner and the love of my life.
Looking at the photos now, I’m amused to find that 19-year-old Lindsay was gawky, awkward, and endearingly shy. To me at the time, though, she was a smoldering blonde, absolutely volcanic. What’s more, the photos themselves were beautiful: They had a serious artistic quality, self-portraits more than selfies. They caught the eye and held it. They played coyly with light and shade. They even had a hint of meta fun: there was one taken inside the photo lab where she worked, and another where she wasn’t even facing the camera.
I rated her Hot, a perfect 10. To my surprise, we matched (she rated me an eight, the angel), and in no time we were chatting. Lindsay was studying fine art photography. She had her own website, where she kept a journal and posted more shots: forests, flowers, abandoned factories, and — my favorite — more of her.
I scoured the Web and used each new fact I found about her to create a fuller picture: the town she was born in (Laurel, Maryland), her school’s name (MICA, the Maryland Institute College of Art). Eventually, I admitted to cyberstalking her. I felt like a creep, but Lindsay cut me off. “I’ve been searching about you, too, mister,” she said, and rattled off a list of facts about me. She’d checked my email address against dozens of sites, figuring out which ones I’d registered on.
I felt like a creep, but Lindsay cut me off. “I’ve been searching about you, too, mister.”
These were among the sweetest words I’d ever heard, yet I was reluctant to see her in person. We scheduled a date, and as the days ticked down my nervousness grew. It’s a scary proposition, to take an online relationship offline. It would be scary even in a world without ax murderers and scammers. In my experience, the more you’ve communicated with someone online, the more disappointed you’ll be by meeting them in person. Things that are the easiest to say on-screen become the most difficult to say face-to-face. Distance favors intimacy: No one talks more openly than when they’re alone in a room, chatting with an unseen someone alone in a different room. Meet that person, however, and you lose your latitude. Your talk becomes safer and tamer, a common conversation on neutral ground.
Online, Lindsay and I had become total confidants, and I was afraid of losing our connection in person. In other words, I was afraid of being rejected.
I shouldn’t have been.
Lindsay — who’d insisted on driving — told me that she’d pick me up at my mother’s condo. The appointed hour found me standing outside in the twilight cold, guiding her by phone through the similarly named, identical-looking streets of my mother’s development. I was keeping an eye out for a gold ’98 Chevy Cavalier, when suddenly I was blinded, struck in the face by a beam of light from the curb. Lindsay was flashing her brights at me across the snow.
“Buckle up.” Those were the first words that Lindsay said to me in person, as I got into her car. Then she said, “What’s the plan?”
It’s then that I realized that despite all the thinking I had been doing about her, I’d done no thinking whatsoever about our destination.
If I’d been in this situation with any other woman, I’d have improvised, covering for myself. But with Lindsay, it was different. With Lindsay, it didn’t matter. She drove us down her favorite road — she had a favorite road — and we talked until we ran out of miles on Guilford and ended up in the parking lot of the Laurel Mall. We just sat in her car and talked.
It was perfection. Talking face-to-face turned out to be just an extension of all our phone calls, emails, and chats. Our first date was a continuation of our first contact online and the start of a conversation that will last as long as we will. We talked about our families, or what was left of them. Lindsay’s parents were also divorced: Her mother and father lived 20 minutes apart, and as a kid Lindsay had been shuttled back and forth between them. She’d lived out of a bag. Mondays, Wednesdays, and Fridays she slept in her room at her mother’s house. Tuesdays, Thursdays, and Saturdays she slept in her room at her father’s house. Sundays were the dramatic day, because she had to choose.
She told me how bad my taste was and criticized my date apparel: a button-down shirt decorated with metallic flames over a wifebeater and jeans (I’m sorry). She told me about the two other guys she was dating, whom she’d already mentioned online, and Machiavelli would’ve blushed at the ways in which I set about undermining them (I’m not sorry). I told her everything, too, including the fact that I wouldn’t be able to talk to her about my work — the work I hadn’t even started. This was ludicrously pretentious, which she made obvious to me by nodding gravely.
I told her I was worried about the upcoming polygraph required for my clearance, and she offered to practice with me — a goofy kind of foreplay. The philosophy she lived by was the perfect training: Say what you want, say who you are, never be ashamed. If they reject you, it’s their problem. I’d never been so comfortable around someone, and I’d never been so willing to be called out for my faults. I even let her take my photo.
I told her I was worried about the upcoming polygraph. The philosophy she lived by was the perfect training: say what you want, say who you are, never be ashamed.
I had her voice in my head on my drive to the NSA’s oddly named Friendship Annex complex for the final interview for my security clearance. I found myself in a windowless room, bound like a hostage to a cheap office chair. Around my chest and stomach were pneumographic tubes that measured my breathing. Finger cuffs on my fingertips measured my electrodermal activity, a blood pressure cuff around my arm measured my heart rate, and a sensor pad on the chair detected my every fidget and shift. All of these devices — wrapped, clamped, cuffed, and belted tightly around me — were connected to the large black polygraph machine placed on the table in front of me.
Behind the table, in a nicer chair, sat the polygrapher. She reminded me of a teacher I once had — and I spent much of the test trying to remember the teacher’s name, or trying not to. She, the polygrapher, began asking questions. The first ones were no-brainers: Was my name Edward Snowden? Was 6/21/83 my date of birth? Then: Had I ever committed a serious crime? Had I ever had a problem with gambling? Had I ever had a problem with alcohol or taken illegal drugs? Had I ever been an agent of a foreign power? Had I ever advocated the violent overthrow of the United States government? The only admissible answers were binary: “Yes” and “No.” I answered “No” a lot, and, before I knew it, the test was over.
I’d passed with flying colors.
As required, I had to answer the series of questions three times in total, and all three times I passed, which meant that not only had I qualified for the TS/SCI, I’d also cleared the “full scope polygraph” — the highest clearance in the land.
I had a girlfriend I loved, and I was on top of the world.
I was 22 years old.
________________________________________________
Excerpted from PERMANENT RECORD by Edward Snowden, published by Metropolitan Books, an imprint of Henry Holt and Company. Copyright ©2019 by Edward Snowden. All rights reserved.
Related:
- Intercepted Podcast: Snowden vs. Trump
- A Conversation on Privacy With Edward Snowden, Noam Chomsky, and Glenn Greenwald
- Edward Snowden Explains How To Reclaim Your Privacy
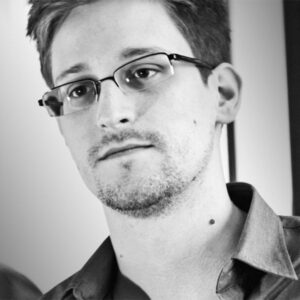 Born in North Carolina in 1983, Edward Snowden worked for the National Security Agency through subcontractor Booz Allen in the NSA’s Oahu (Honolulu) office, where he began collecting top-secret documents regarding NSA surveillance practices that he found disturbing. After he fled to Hong Kong newspapers began printing documents that he leaked to them, many detailing invasive spying practices against American citizens, world leaders, corporations and foreign governments through metadata collection of phone calls, email messages, social media activities, plus dissemination of malicious software and viruses throughout computers worldwide. The U.S. has charged Snowden under the Espionage Act but he is hailed around the world as a hero. He remains in exile in Russia, with the U.S. government working on extradition. Snowden is a director of the Freedom of the Press Foundation.
Born in North Carolina in 1983, Edward Snowden worked for the National Security Agency through subcontractor Booz Allen in the NSA’s Oahu (Honolulu) office, where he began collecting top-secret documents regarding NSA surveillance practices that he found disturbing. After he fled to Hong Kong newspapers began printing documents that he leaked to them, many detailing invasive spying practices against American citizens, world leaders, corporations and foreign governments through metadata collection of phone calls, email messages, social media activities, plus dissemination of malicious software and viruses throughout computers worldwide. The U.S. has charged Snowden under the Espionage Act but he is hailed around the world as a hero. He remains in exile in Russia, with the U.S. government working on extradition. Snowden is a director of the Freedom of the Press Foundation.
Go to Original – theintercept.com
Tags: 1984, Activism, Big Brother, Big tech, Capitalism, Conflict, Control, Democracy, Development, Dictatorship, Economics, Edward Snowden, Freedom, Freedom of the press, Human Rights, Journalism, Justice, Marketing, Media, Politics, Power, Privacy rights, Progress, Social justice, Spying, Surveillance, Technology, USA, Violence, West, World
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.
Read more
Click here to go to the current weekly digest or pick another article:
MEDIA:
- Freedom (of the Press) and Peace Are Not Ideological but Scientific Facts
- Paramount’s Purchase of CNN Heralds a New Trump-Friendly Media Empire
- Amy Goodman on the Media’s “Access of Evil”
WHISTLEBLOWING - SURVEILLANCE: