Source Code Similarities: Experts Unmask ‘Regin’ Trojan as NSA Tool
WHISTLEBLOWING - SURVEILLANCE, 2 Feb 2015
Marcel Rosenbach, Hilmar Schmundt and Christian Stöcker – Der Spiegel
Just weeks ago, SPIEGEL published the source code of an NSA malware program known internally as QWERTY. Now, experts have found that it is none other than the notorious trojan Regin, used in dozens of cyber attacks around the world.
Earlier this month, SPIEGEL International published an article based on the trove of documents made available by whistleblower Edward Snowden describing the increasingly complex digital weapons being developed by intelligence services in the US and elsewhere. Concurrently, several documents were published as well as the source code of a sample malware program called QWERTY found in the Snowden archive.
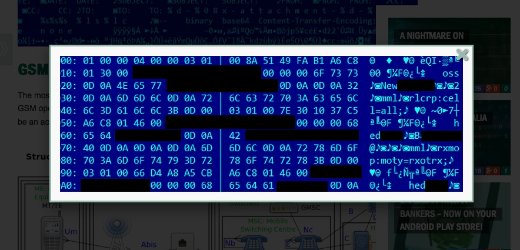
For most readers, that source code was little more than 11 pages of impenetrable columns of seemingly random characters. But experts with the Russian IT security company Kaspersky compared the code with malware programs they have on file. What they found were clear similarities with an elaborate cyber-weapon that has been making international headlines since November of last year.
Last fall, Kaspersky and the US security company Symantec both reported for the first time the discovery of a cyber-weapon system which they christened “Regin”. According to Kaspersky, the malware had already been in circulation for 10 years and had been deployed against targets in at least 14 countries, including Germany, Belgium and Brazil but also India and Indonesia.
Symantec spoke of a “highly complex” threat. Many of the targets were in the telecommunications sector, but others included energy companies and airlines. Both Symantec and Kaspersky did not shy away from superlatives when describing the malware program, calling it a “top-tier espionage tool” and the most dangerous cyber-weapon since Stuxnet, the notorious malware program used to attack the Iranian nuclear program.
“We are certain that we are looking at the keylogger-module from Regin,” Costin Raiu, head of research for Kaspersky, said of the code published by SPIEGEL. A keylogger is a program that can record keys struck on a keyboard — thus logging sensitive information such as passwords, email addresses and text documents — and then send that information back to the malware programmer.
“Pursuant to our technical analysis, QWERTY is identical with the Regin plug-in 50251,” Raiu says. In addition, the analysis revealed that Regin is apparently an attack platform that can be used by several different institutions in several different countries. Kaspersky published its findings in a blog post on Tuesday.
The new analysis provides clear proof that Regin is in fact the cyber-attack platform belonging to the Five Eyes alliance, which includes the US, Britain, Canada, Australia and New Zealand. Neither Kaspersky nor Symantec commented directly on the likely creator of Regin. But there can be little room left for doubt regarding the malware’s origin.
- The source code excerpt published by SPIEGEL comes straight from the Snowden archive.
- Regin was also apparently involved in the attack on the Belgian telecommunications firm Belgacom. And Belgacom, as SPIEGEL reported in the summer of 2013, was a target of the British intelligence agency GCHQ. Ronald Prins, head of the Dutch security company Fox IT, which analyzed the attack on Belgacom, told SPIEGEL ONLINE in the summer of 2011 that Regin appeared to be a tool belonging to the NSA and GCHQ.
There are also additional clues pointing to Regin being a Five Eyes tool:
- In the QWERTY code, there are numerous references to cricket, a sport that enjoys extreme popularity in the Commonwealth.
- There are many similarities with the cyber-weapons system that the intelligence agencies call “Warriorpride” in the Snowden documents.
- The targets thus far known are consistent with Five Eyes surveillance targets as outlined in the Snowden documents.
Photo Gallery: Operation Socialist
In the last several years, Regin has been exposed as the cyber-weapon behind a number of digital attacks:
- The attack on the partially state-owned company Belgacom, as mentioned above.
- A serious cyber-attack on the European Commission in 2011. The deputy head of Germany’s Federal Office for Information Security, Andreas Könen, told SPIEGEL at the end of last December that, “we have reconstructed that; there are clear congruencies.”
- The Austrian newspaper Der Standard, citing anonymous sources, reported last November that malware code from the Regin family had been found in the network of the International Atomic Energy Agency, based in Vienna.
- Germany’s Bild newspaper also reported a Regin infection in the computer of a member of the department for European affairs in Angela Merkel’s Chancellery. According to the paper, the malware was found on the woman’s private computer. The Federal Office for Information Security says that Regin has not yet been found on official German government computers.
It seems likely that more Regin discoveries will be made. Kaspersky alone, says Raiu, has found the malware in computers belonging to 27 international companies, governments and private persons.
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.
Read more
Click here to go to the current weekly digest or pick another article:
WHISTLEBLOWING - SURVEILLANCE: